

Ukraine’s Security Service (SBU) said it had joined the FBI, Polish counter-intelligence and European law-enforcement partners in a coordinated cyber operation against what it described as a large-scale Russian espionage campaign built around compromised Wi-Fi routers. The operation targeted an intelligence network that had been harvesting data from domestic and office internet devices across Ukraine, the European Union and the United States.
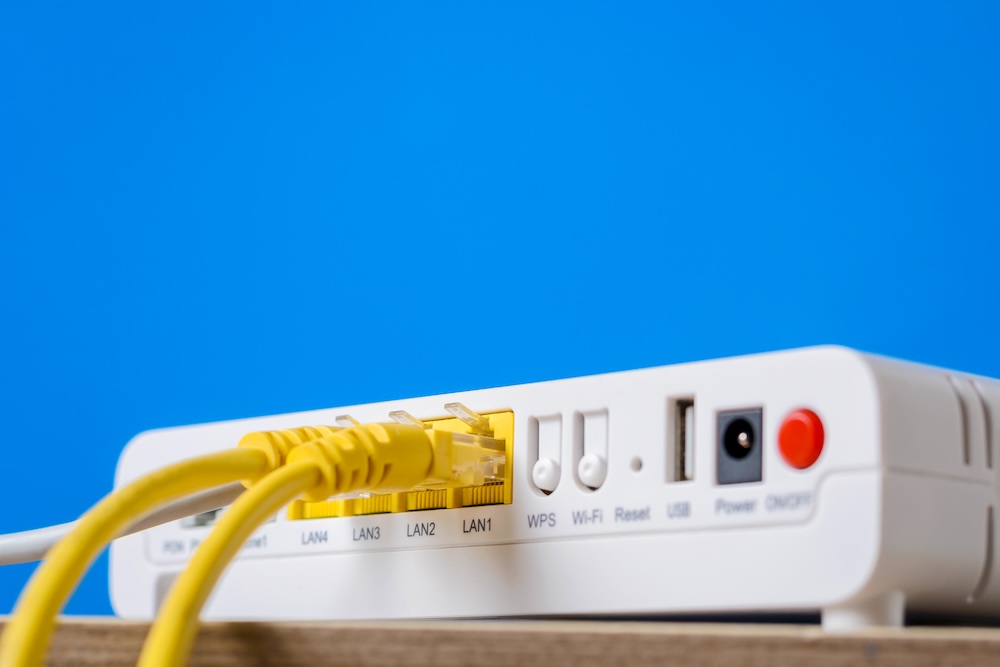
The reported method was technically straightforward but operationally significant. Investigators said Russian operators gained access to routers with outdated or weak security settings and then altered DNS configurations to reroute internet traffic through infrastructure under their control. Once that was done, the attackers were able to position themselves between users and the services they were trying to reach, creating conditions for what cyber agencies describe as adversary-in-the-middle attacks.
That approach can allow hostile actors to collect passwords, authentication tokens, email-related credentials and other information moving across a network. The UK’s National Cyber Security Centre said in its advisory that APT28, which it attributes to Russia’s GRU Unit 26165, had been exploiting vulnerable routers to overwrite DHCP and DNS settings and redirect traffic through attacker-controlled servers. The NCSC added that the activity appeared opportunistic at first, with a wide pool of victims compromised before attention narrowed to users considered to be of intelligence value.
The SBU said the Russian operation had focused in particular on data linked to state institutions, military personnel and companies in the defence-industrial sector. The implication is that ordinary networking equipment, often overlooked by users once installed, was turned into an access point for strategic intelligence collection. In practice, this makes poorly maintained routers an attractive target: they are widespread, frequently left with default settings or old firmware, and often sit outside the regular security controls applied to larger enterprise systems.
Ukrainian authorities said that more than 100 servers were blocked during the joint operation and that hundreds of routers in Ukraine were removed from hostile control. The US Department of Justice said separately that, in the United States, the FBI conducted a court-authorised technical disruption designed to reset DNS settings on compromised routers, remove malicious resolvers and prevent continued exploitation. According to the Department of Justice, affected devices had been used by GRU actors in the US and elsewhere for espionage purposes.
The scale of the case suggests a broad intelligence-gathering effort rather than a narrowly targeted intrusion. Reuters reported, citing the Justice Department, that the disruption concerned a Russian military-run DNS hijacking network and that the campaign formed part of what US officials called “Operation Masquerade”. The same report said the infrastructure had been used to intercept traffic and gather sensitive data from government, military and critical infrastructure-related targets.
The case also underlines a wider trend in Russian cyber operations: the use of basic internet infrastructure and edge devices as a low-cost means of access. Rather than relying only on high-end bespoke intrusions, operators can exploit vulnerable consumer and small-office hardware at scale, then sort through the resulting data for individuals or organisations of interest. The NCSC advisory noted that at least some activity involved TP-Link models, including the WR841N, and that compromised MikroTik and TP-Link routers were used to feed requests towards malicious infrastructure.
For users and organisations, the practical message is not especially new, but it is increasingly important. The SBU urged people to inspect their router settings, update firmware, change passwords and disable remote administration unless it is necessary. Where a device is no longer supported by its manufacturer and no longer receives security patches, the recommendation was to replace it. The FBI and DOJ guidance makes the same point, stressing that router owners should secure their devices and apply remediation steps set out by the authorities.
The investigation remains ongoing, and Ukrainian authorities said efforts continue to identify all those involved. What has already emerged, however, is a clear reminder that in a period of sustained hybrid confrontation, even routine home and office networking equipment can become part of a transnational intelligence operation.
Zaluzhnyi says Black Sea control is central to Ukraine’s survival and Europe’s security