

Lithuania has charged 13 people in connection with two alleged attempted murders in Vilnius linked to Russia’s GRU military intelligence service, in a case that adds to wider European concerns over hostile activity directed at Ukraine’s supporters and critical infrastructure.
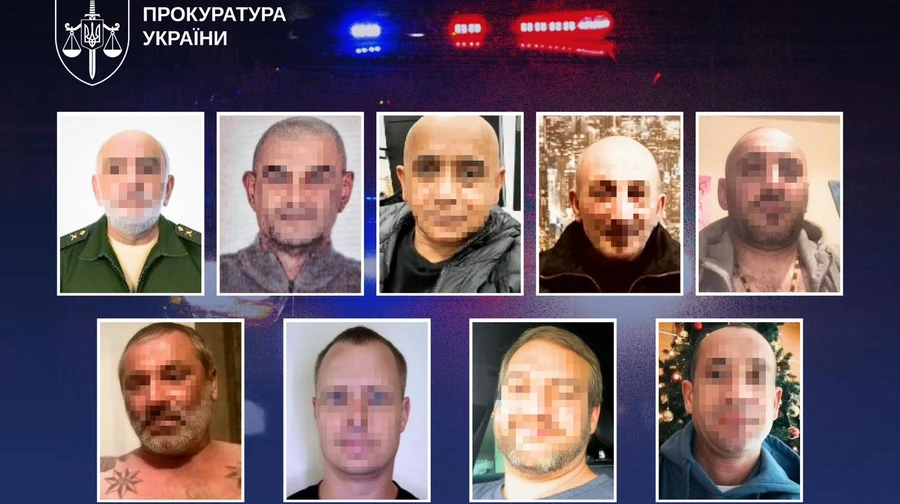
The suspects, from several countries, are accused of involvement in plots to kill a Lithuanian citizen and a Russian citizen in the Lithuanian capital. The case was outlined by Lithuania’s criminal police chief, Saulius Briginas, after an investigation that began early last year and led to arrests in March. The charges announced on 27 April allege that those seeking to carry out the killings acted in the interests of Russia’s military intelligence agency.
The alleged targets were a Lithuanian activist supporting Ukraine and a Russian dissident linked to the Bashkir minority. The case therefore appears to sit at the intersection of several security concerns: intimidation of pro-Ukraine voices, pressure on Russian opposition figures abroad, and the use of criminal or semi-criminal intermediaries for operations inside EU and NATO territory.
The Lithuanian investigation also links the alleged network to other hostile activity in Europe. The suspects are accused of involvement in an arson attack on military equipment destined for Ukraine in Bulgaria and espionage connected to military activity in Greece. Ukrainian authorities have also described the group as a Russian intelligence network involved in planning attacks against Ukrainian journalists and an intelligence official.
For Lithuania, the case is not an isolated law-enforcement matter. It comes against the background of repeated Baltic warnings that Russia is using sabotage, cyber activity, disinformation, arson and proxy operations below the threshold of conventional military conflict. Vilnius has been one of Kyiv’s strongest supporters since Russia’s full-scale invasion of Ukraine, making it a prominent target for pressure and intimidation.
Lithuanian authorities have previously linked other incidents to Russian military intelligence. In January, officials said the GRU was behind an attempted arson attack in 2024 on a Lithuanian facility supplying radio wave scanners to Ukraine’s military. That case involved suspects from several countries and was presented by Lithuanian officials as part of a broader pattern of Russian-directed sabotage across Europe.
The present case is more serious because of the alleged move from disruption and property damage to planned assassinations. If proven, the charges would indicate that Russian-linked networks are prepared to target individuals on EU territory, including activists and dissidents whose public positions conflict with Moscow’s interests.
The operational pattern described by investigators is also significant. The use of foreign nationals, criminal contacts and cross-border activity can make attribution slower and more difficult. It can also allow a state actor to create distance between itself and the people carrying out the operation. That model is consistent with the broader category of hybrid activity now being tracked by European security services.
For NATO, the Lithuanian case raises practical questions about internal security and deterrence. Article 5 is designed for armed attack, but much of the pressure currently directed at alliance members is taking place in the space between criminality, intelligence work and sabotage. The challenge for governments is to respond firmly without treating every incident as a conventional military escalation.
That makes police cooperation, counter-intelligence, border control and judicial coordination increasingly important. A sabotage network may operate across several jurisdictions, use different nationalities and target assets or individuals connected to the war in Ukraine. Effective response therefore depends on rapid information-sharing between national authorities, prosecutors and intelligence services.
There is also a defence-industry dimension. The alleged Bulgarian arson attack concerned military equipment bound for Ukraine. As European states increase ammunition, drone, air-defence and logistics support for Kyiv, supply chains, depots, transport nodes and commercial contractors are likely to remain attractive targets for disruption. Protecting those networks is now part of European defence resilience.
Russia has repeatedly denied involvement in sabotage and hostile operations in Europe. The Lithuanian charges will now need to be tested through legal proceedings, and the defendants are entitled to the presumption of innocence. The political significance of the case, however, is already clear: Baltic authorities are treating such incidents as part of a wider security campaign rather than as disconnected criminal acts.
For Lithuania and its allies, the immediate issue is not only the prosecution of those charged. It is whether European states can identify, disrupt and deter networks that operate below the level of open conflict while still producing strategic effects. The Vilnius case suggests that the line between domestic security and defence policy is becoming increasingly difficult to separate.